
Education & development
How-tos
Screen time
Online safety guides, app reviews, and wellbeing-focused practical advice, designed to take the stress out of tech and help you connect with your family.
Discover the guides, advice, and support parents like you are searching for.



Sign up for our free monthly newsletter to get in-depth guides, online safety advice, and the latest in digital parenting - straight to your inbox.

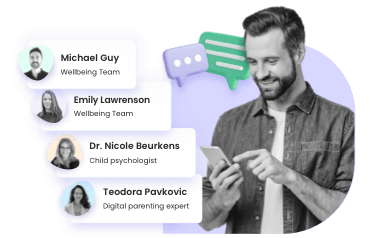
See questions answered by parenting, psychology and tech experts.
Mental health & wellbeing
View all


App reviews
View allHow-tos
View all
Should I get my child a phone? The complete guide
Answered by: Dr. Nicole Beurkens
See answer
What is brain rot? A parent’s guide
Answered by: Emily Lawrenson
See answer
Your child’s AI friend? A parents’ guide to companion bots
Answered by: Teodora Pavkovic
See answer